We all have that one blinking box tucked behind a dusty curtain, quietly powering our late-night streaming and remote work. However, recent 2026 data from Forescout’s Riskiest Connected Devices report suggests your router might actually be the most hackable gadget in your home, often carrying double the vulnerabilities of a standard computer. It is a sobering thought for anyone relying on a stable, private connection.
The Burden of Factory Credentials

Many people never change the default “admin” password provided at setup. Research by ET Edge Insights in 2026 highlights that these factory settings remain a primary gateway for automated botnet intrusions.
Outdated Firmware Risk Factors

Routers don’t always have automatic updates, as we can see on our smartphones. This manual gap leaves critical security holes wide open, as many users simply forget to check for available software patches.
Foreign Manufacturing Security Concerns

In March 2026, the FCC added various foreign-produced consumer routers to its Covered List. This move reflects growing national security anxieties regarding potential supply chain vulnerabilities within certain imported networking hardware.
The Rise of AI Exploits

Artificial intelligence is now being used to automate the “fingerprinting” of home devices. According to 2026 reports, AI tools can identify a router’s model and deploy specific exploits in mere minutes.
End-of-Life Hardware Traps
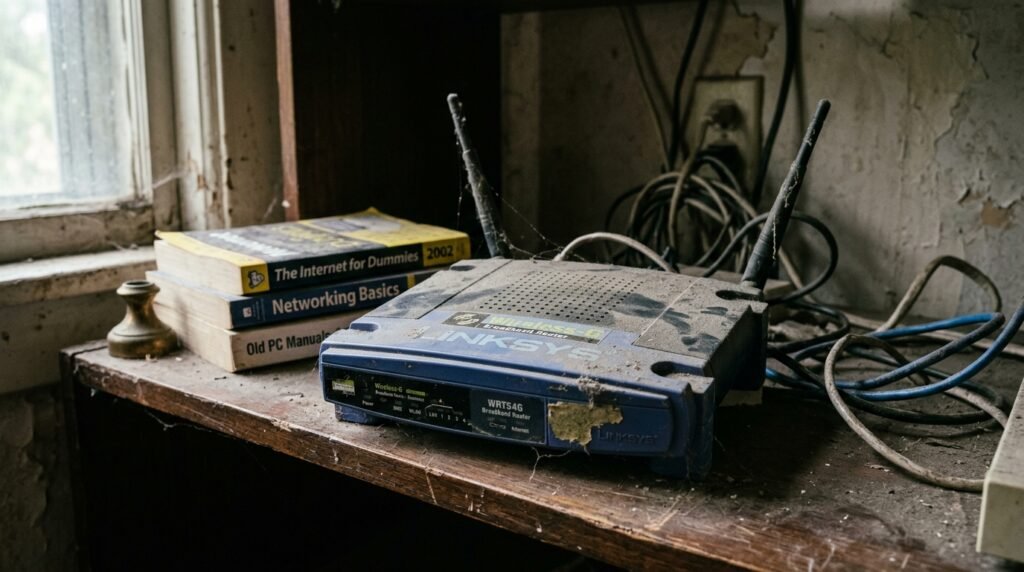
Old routers, no longer supported by the manufacturer, are like sitting ducks. A device once declared as “end of life” can still be used, but it will always be susceptible to any new threats discovered.
Unauthenticated Command Injection Flaws

Some popular consumer models have suffered from “unauthenticated command injection” vulnerabilities. This specific flaw might allow a stranger to run code on your hardware without ever needing to know your password.
Digital Mules and Proxy Risks

Your home connection could be used to hide someone else’s tracks. The FBI’s 2026 AVRecon report notes that compromised routers are often sold as “residential proxies” to mask criminal activity.
Exposed Remote Management Portals

Keeping the “Remote Management” feature toggled on is often a mistake. This setting potentially allows anyone on the internet to find your login page, making the device an easy target for scanners.
Legacy Protocol Vulnerabilities

Many devices are still running older protocols such as UPnP or Telnet as a compatibility measure. These old benchmarks are inadequate to withstand today’s sophisticated forms of cyberattacks.
Hardware Backdoor Suspicions
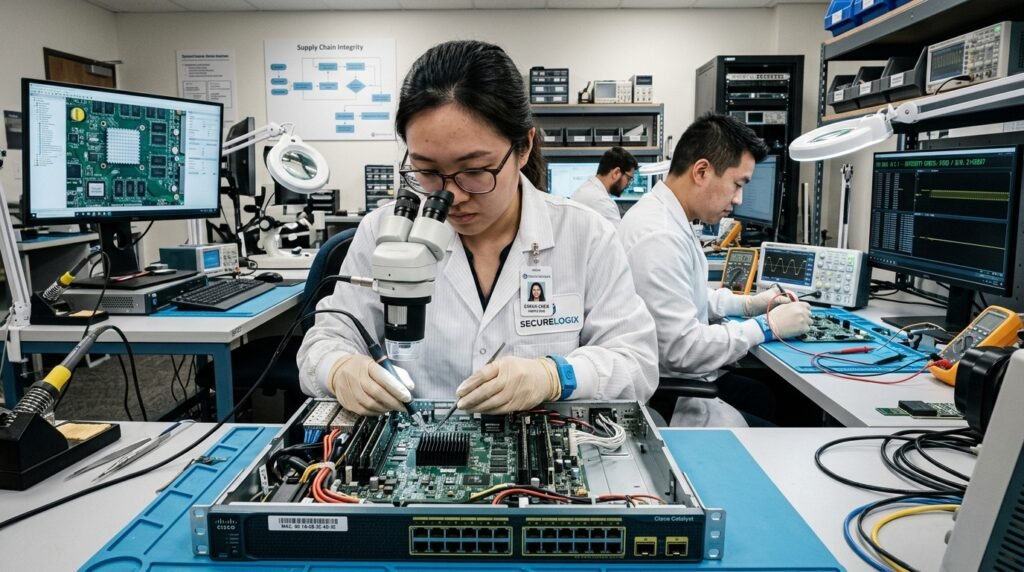
While hard evidence of intentional backdoors is rare, the 2026 National Security Determination suggests the supply chain itself is a risk. This uncertainty makes the origin of your hardware more relevant.
Middleman Attacks on Traffic

If the router becomes compromised, a malicious entity can be in the middle of your traffic. This could lead them to view unencrypted data or lead you to fake, look-alike websites.
Botnets and DDoS Participation

Your router might be part of a “zombie” army without you knowing. High-speed home connections are perfect for DDoS attacks, where thousands of hijacked devices overwhelm a single target’s web server.
