People find phone privacy to be a complicated matter, which makes them depend on their assumptions rather than learning about actual phone operations. People develop their daily phone usage patterns through their minor mistakes with apps and setting knowledge. The myths exist because technology develops at a fast pace, which creates challenges for people to handle. The process of clearing these misunderstandings will help people make better decisions about their phone usage throughout their daily activities.
Privacy Settings Are “Set and Forget”

People think that privacy settings remain perfect after they make their initial changes. The actual situation involves apps and updates which introduce different features to users after they install the software. People should check their settings because their personal preferences and device usage patterns will develop over time.
Private Browsing Means Invisible Browsing

The private and incognito browsing modes only prevent local history from being recorded. Users cannot hide their online activities from websites and networks and service providers. People need to understand this concept because it enables them to use these features with more accurate expectations.
Only Unknown Apps Access Data
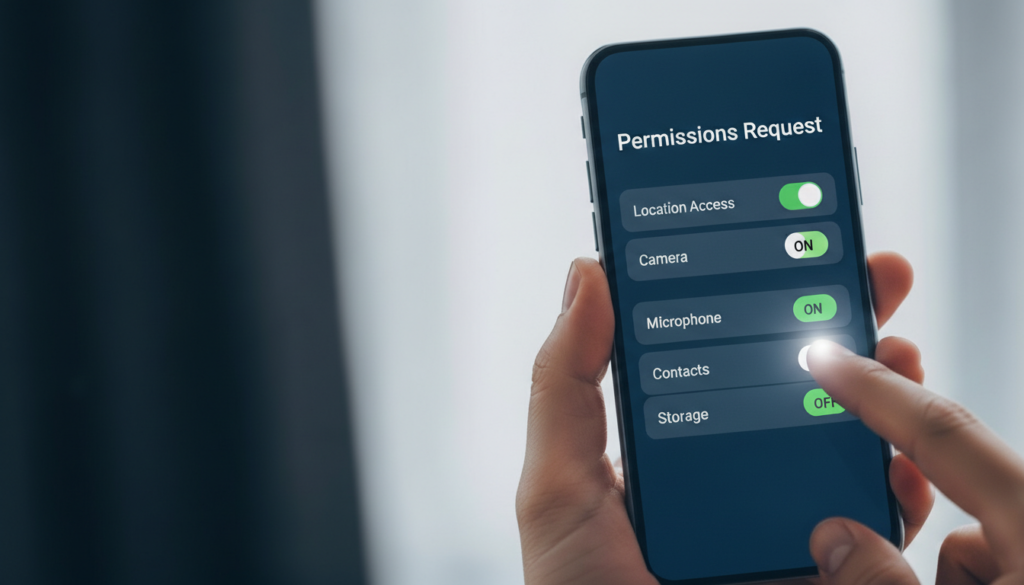
Apps that people use frequently need to ask for permissions because those permissions enable their primary functions. Users should obtain access to data because it enables them to experience various features. Users can protect themselves by reviewing their app permissions to maintain control over their information while enjoying the app advantages.
Turning Off Location Solves Everything

Location services use multiple technologies, such as GPS systems. The system uses Wi-Fi and Bluetooth signals together with app activity for location determination. People can better control their location sharing activities when they understand how these various signals operate together.
Strong Passwords Handle All Security

People need passwords to protect their accounts, but phone privacy protection requires users to monitor app activity and system updates and device settings. The implementation of a comprehensive solution will enable users to maintain better control over their personal information.
Public Wi-Fi Is Always Risky

Public networks showcase different security systems which include basic security systems and complete network accessibility. Network users maintain their online security by using three methods which include understanding the risks and using secure internet connections from public locations.
Deleting Apps Deletes All Data
When users delete an application from their device, the program disappears from their device but certain information continues to connect with their online accounts. Users can understand which information will remain saved in other locations by examining their account settings.
Phones Listen Constantly

Voice assistants respond to wake words rather than continuous listening. Users can build trust in product functions by understanding how these tools operate based on their activation methods.
Privacy Requires Technical Expertise

Phone privacy control does not require users to possess advanced computer knowledge. People can keep their personal information secure by following simple security practices which include checking permissions and updating programs and monitoring notifications.
